DNS is the internet’s address book. Without it, you’d be typing 187.124.233.248 instead of stackoftruths.com.
It’s everywhere. It’s trusted. And that’s exactly why attackers love it.
What Makes DNS a Target
DNS traffic is rarely blocked. Firewalls let it through because without it, nothing works. Attackers exploit this trust by hiding malicious activity inside DNS queries.
1. DNS Tunneling
Attackers encode stolen data into DNS requests. Each query looks like a normal lookup — stolen-api-key.attacker.com. The attacker’s server decodes it on the other end. Exfiltration without a single suspicious TCP connection.
2. Command & Control (C2)
Compromised machines check in with DNS. A query to update.attacker.com might mean “I’m alive.” A response could be a command. No persistent connection, no obvious C2 channel.
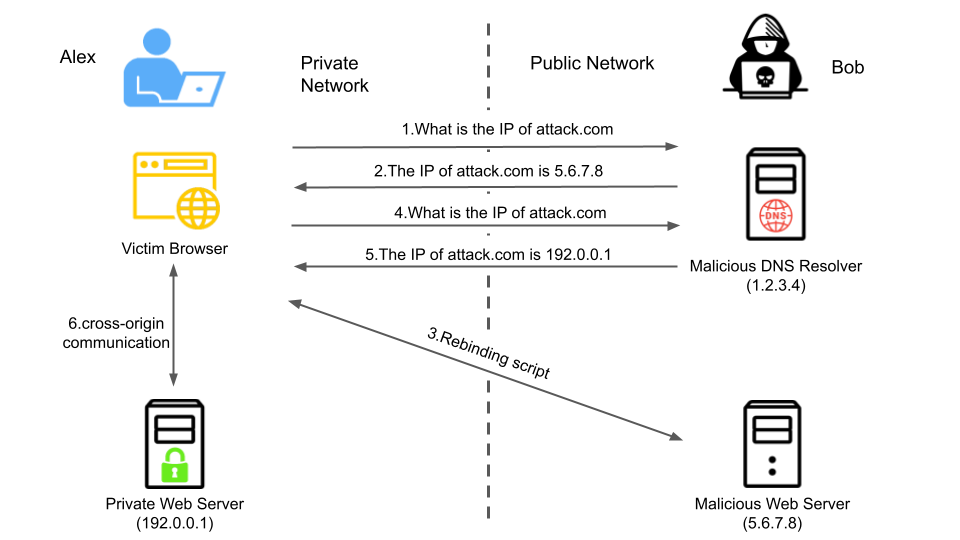
3. DNS Poisoning / Cache Poisoning
Injecting false DNS records. Users trying to visit stackoftruths.com end up at a fake site. Credentials stolen. Sessions hijacked. The user never sees it coming.
4. Data Exfiltration
Sensitive data — API keys, customer records, internal documents — packed into subdomains and sent out one query at a time. Slow, but hard to detect.
How Attackers Hide
DNS traffic is noisy. Your average network sees thousands of lookups per minute. Attackers blend in.
They use legitimate domains. They use encryption (DoT, DoH). They mimic normal traffic patterns. The signals are there, but you have to know what to look for.
Catching DNS Abuse
Wireshark is your first stop. Filter for DNS. Look for:
- Unusually long subdomains — more than 50 characters often means tunneling
- High query volume to a single domain
- NXDOMAIN responses — could be reconnaissance or exfiltration retries
- DNS queries at odd hours — systems phoning home when no one’s around
Protecting Your Network
- Monitor DNS logs — not just for failures, but for patterns
- Use DNS over TLS (DoT) or DNS over HTTPS (DoH) — prevent snooping, but also monitor what’s leaving
- Block known malicious domains — threat intelligence feeds help
- Rate limit DNS queries — tunneling needs volume
- Audit your AI agents — they make DNS calls too. Security Sentinel monitors what your agents are reaching out to.
What This Means for AI Agents
If you’re running AI agents — OpenClaw, custom bots, anything that makes external calls — DNS becomes part of your threat model.
We run 6 agents on a VPS. They need to make DNS queries to function. But we monitor them. If an agent suddenly starts resolving domains at 3 AM with long, suspicious subdomains, that’s a problem. Security Sentinel flags it before it becomes a breach.
Closing Thoughts
DNS is the protocol you depend on and the protocol attackers exploit. It’s not enough to have it working. You have to watch it.
The same principle applies to your agents. Trust is not a control. Visibility is.
🦞 Stacking truths daily. One protocol at a time.





Leave a Reply