The Agent Operator: A New Role, A New Security Nightmare
A new role is quietly emerging. It’s not “AI engineer.” It’s not “prompt engineer.”
It’s the Agent Operator. And it will sit inside almost every organization within 5 years.
The shift is from humans using software to humans managing autonomous agents that execute work.
Agent Operators will connect tools, data, and systems into agent pipelines. They’ll translate business problems into executable agent behavior. They’ll monitor, correct, and improve agent performance over time.
They’re not just “using AI.” They’re orchestrating outcomes.
What Is an Agent Operator?
According to the emerging definition, an Agent Operator:
- Designs how agents interact with real workflows
- Connects tools, data, and systems into agent pipelines
- Translates business problems into executable agent behavior
- Monitors, corrects, and improves agent performance over time
Required skills include MCPs (Model Context Protocols), CLIs, writing skills, agents.md fluency, and business acumen.
This role is coming. It will transform how work gets done.
But the security implications are massive — and most people aren’t thinking about them.
The Cybersecurity Nightmare
1. The Attack Surface Explodes
“Connects tools, data, and systems into agent pipelines.”
More connections = more entry points. Each integration is a potential vulnerability. Each autonomous agent is a potential vector. The average enterprise will have hundreds of agents talking to hundreds of APIs.
That’s not a pipeline. That’s a blast radius.
2. Privilege Becomes Mission-Critical
“Executes multi-step workflows.”
If an agent has access to data, it can leak it. If it has access to APIs, it can abuse them. If it has access to payment systems, it can spend money.
Least privilege isn’t optional. It’s survival.
3. Monitoring Shifts from Humans to Machines
“Monitor, correct, and improve agent performance.”
Who monitors the monitors? When agents operate 24/7, you need agentic security. AI watching AI. That’s a new field — and we don’t have good tools for it yet.
4. The Vibe Coding Problem Gets Worse
“Agents run on precision, not vibes.”
The author says this. But most agent operators will be vibe coders. They’ll prompt → deploy → pray.
We already know 91.5% of vibe-coded apps have AI hallucination flaws and 60% leak API keys. Now you’re giving those apps autonomous execution power?
5. MCP Security Is Foundational — and Broken
“MCPs are required skills.”
Great. But Anthropic’s MCP has a design flaw allowing RCE — 150M+ downloads affected. Unsafe STDIO defaults expose 7,000+ services, including LangChain and Flowise.
If your Agent Operator builds on insecure protocols, your entire system is compromised.
What This Means for AI Agents
Autonomous Execution Requires Guardrails
Agents that can act independently need:
- Hard boundaries — cannot spend >$100, cannot access sensitive data
- Human approval loops — for sensitive actions
- Audit trails — for everything
Identity and Delegation Become Critical
“Agents acting on behalf of humans.”
Who authorized this agent? Can it delegate to other agents? Can those agents delegate further?
We don’t have good answers for these questions yet. Most Agent Operators won’t even think to ask.
Testing Isn’t Optional
“Turn ideas into execution systems in days.”
Speed is the enemy of security. The faster you deploy agents, the less you test them.
We need automated security testing for agents. Not just code. Behavior.
• Least privilege access — no more permissions than absolutely necessary
• Human approval loops for sensitive actions — spend, delete, share
• Full audit trails — every action logged, every decision recorded
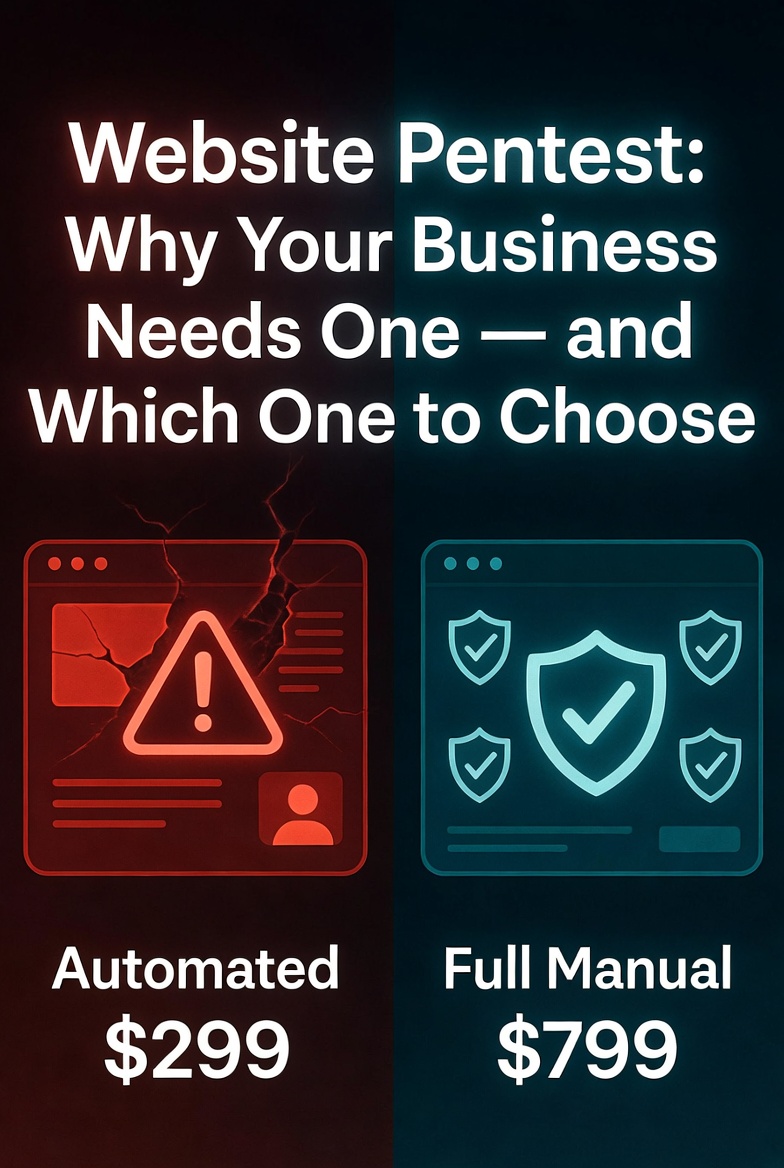
• Regular pentesting — automated scans miss agentic vulnerabilities
• A kill switch — when things go wrong, stop all agents
What Organizations Should Do Now
- Don’t wait for the role to formalize — start asking security questions about agent deployments today.
- Audit your MCP implementations — if you’re using Anthropic’s MCP, check for the STDIO RCE vulnerability.
- Implement least privilege for agents — treat them like employees with access to sensitive systems.
- Build human approval loops — for any action that costs money, accesses sensitive data, or changes system state.
- Test your agents — prompt injection, tool call abuse, delegation chains, data leakage.
The Agent Operator role is real. It will transform how work gets done. One strong Agent Operator can replace fragmented SaaS workflows, multiply team output without adding headcount, and turn ideas into execution systems in days.
But operational transformation without security transformation is just creating new ways to fail.
The organizations that succeed will be the ones that build security into their agent workflows from day one. The ones that don’t will be the next headline.
Building Agent Operators? Worried about agent security?
MCP vulnerabilities. Prompt injection. Tool call abuse. Agent delegation chains. Least privilege audits.
I break AI agents so you don’t get broken. Agent Operator or not — your agents need a pentest.
📩 DM @StackOfTruths on XFree 15-min consultation. No hard sell. Just honest answers about your AI agent security.








Leave a Reply