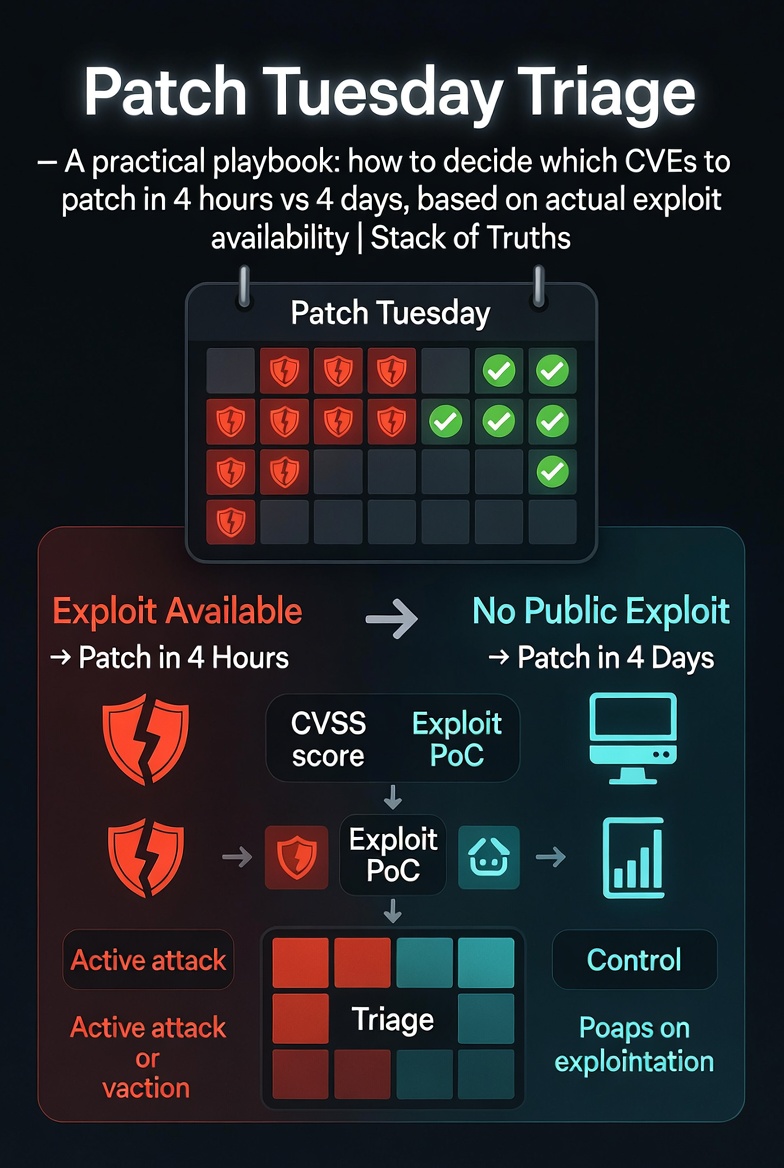
Patch Tuesday Triage — 4 hours vs 4 days
Patch Tuesday drops 50–150 CVEs. Your team has 4 hours of real attention span.
Most security teams do one of two things:
- Panic-patch everything → break production, burn out engineers
- Patch nothing → get pwned by something that had a public exploit on day zero
There’s a third way. It’s called exploit-based triage.
Not all CVEs are created equal. 80% are noise. 15% matter in specific environments. 5% will get you pwned if you don’t patch them today.
Your job isn’t to patch everything. It’s to find the 5%.
The 4‑Hour List (Patch Now)
These get patched within 4 hours. No exceptions.
The 4‑Day List (Schedule a Window)
These get patched within 4 days. Important, but not burning down right now.
The Defer List (Patch Eventually)
These can wait for the monthly patch cycle. Or never. Most teams over-patch these.
- Local DoS (CVSS 5–6) — annoying but not lethal
- Information disclosure (low impact) — unless it’s customer data
- CVSS 4 and below — unless chained with something else
- Vulnerabilities in components you don’t actually use
Defense in depth doesn’t mean patch everything. It means mitigating what you can’t patch.
If you can’t patch the 4‑day list in 4 days, put a WAF rule on it. Restrict access. Monitor logs. That’s defense.
The Decision Flowchart (Cheat Sheet)
Tools to Make This Actually Work
You can’t triage manually. Use these:
| Source | What It Gives You | URL |
|---|---|---|
| CISA KEV | Actively exploited CVEs | cisa.gov/known-exploited-vulnerabilities-catalog |
| EPSS | Probability of exploitation (0–1) | first.org/epss |
| Exploit-DB | Public exploit code | exploit-db.com |
| Twitter/X | Real-time chatter (follow researchers) | @s4dbrd, @SwiftOnSecurity, @GossiTheDog |
| NVD | CVSS scores + references | nvd.nist.gov |
What About Zero-Days?
Same rules apply — but faster.
- Public PoC drops at 2pm? Patch window starts at 2pm.
- No exploit? No active targeting? You have time to test.
- Log4j-style chaos? That’s not triage. That’s incident response. Different playbook.
Your team can’t patch 100 CVEs in a week. Stop trying.
Find the 5% with public exploits or active targeting. Patch those.
The rest can wait. Your production stability will thank you.
And when you’re wrong? That’s what incident response is for.
One More Thing
Triage tells you what to patch. It doesn’t tell you how to patch without breaking things.
That’s a separate problem. But if you’re still reading? You’re already ahead of the teams panic-patching Adobe Reader into production at 4pm on Tuesday.
Need someone to break your stuff before Patch Tuesday ruins it?
Website pentest: $299. AI agent pentest: $750. Full manual audit: $799.
📩 DM @StackOfTruths on XFree 15-min consultation. No hard sell. Just honest answers about your security backlog.










Leave a Reply